SIILO SECURITY STANDARDS
Prioritise patient data security
With the increasing prevalence of commercial messenger apps in clinical settings, it’s more important than ever to keep patient data safe when communicating. That’s why we developed a secure collaboration application that’s 100% confidential and secure.

Minimise compliance risks
Siilo has been built by design to make sure that the privacy of our users’ data is protected, therefore we endeavor to implement processes and measures that meet the highest security standards in healthcare. Siilo is certified against the ISO 27001 standards and NEN 7510, 7512 & 7513, is C5 Type 1 attested and renews each year its submissions with the NHS DSP Toolkit and Information Governance.
Looking for detailed information on our security protocols? Find our certifications and security and compliance documents listed below:
> Security White Paper
> Processor Agreement


End-to-end encryption
Data privacy is guaranteed through end-to-end encryption. This means that no third parties are able to access messages, photos, videos, or files that users exchange on Siilo. Video and voice calls made over Siilo are also end-to-end encrypted.
Secure Camera and Siilo Media
The Secure Camera tool allows users to take photos and videos that are immediately stored within Siilo Media located in the Profile tab. This ensures that sensitive photos and videos of patient information are not locally stored on devices or in personal services such as Apple iCloud, Google Drive, or Dropbox.
Automatic message deletion
Messages sent on Siilo are ephemeral, meaning they will automatically be deleted after 30 days, unless explicitly kept. If your phone is lost or stolen, Siilo’s remote wipe functionality allows you to delete all data still present on the app.

Mandatory Passcode
When installing Siilo, users are required to create a 5‑digit PIN code. This is an extra layer of protection for Siilo’s data. After creating a PIN code, fingerprint or facial recognition can also be activated to access the app.
Backup & Restore
The Siilo Backup & Restore code is a unique sequence of letters and numbers generated for you upon registration. It allows you to preserve and recover your data in the event of a lost or updated device. Siilo only restores account data once there is a confirmed match between the Backup & Restore code and your account. The code can be downloaded from Siilo Web and kept in a secure place for safe keeping.
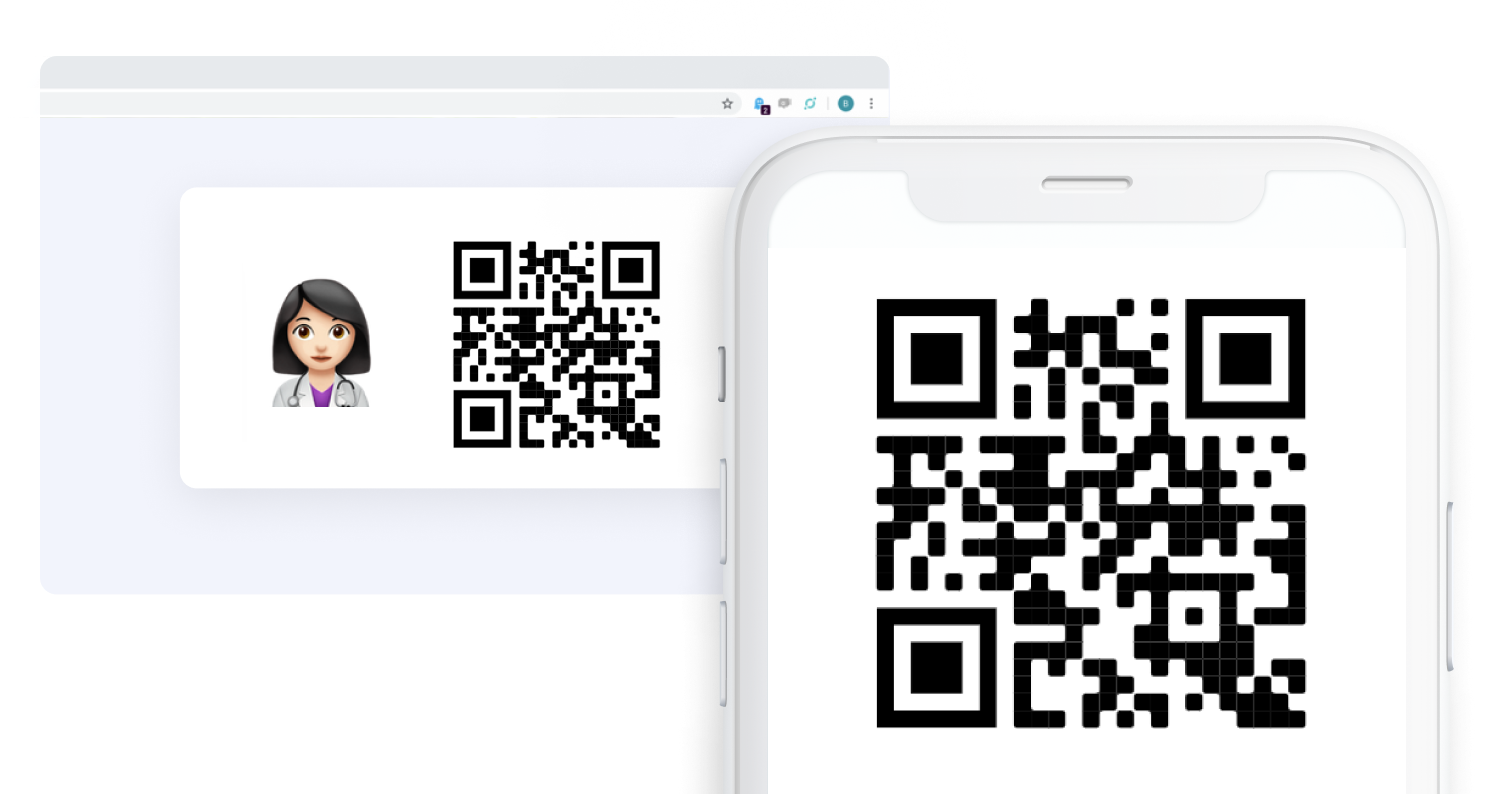
Secure desktop collaboration
Users must scan a QR code using the Siilo mobile app to open the in-browser version of Siilo. Additional features, like an automatic privacy screen and a notification censoring option, make Siilo Web a secure method of collaboration on desktop.
Switch your teams to Siilo
- Download the Siilo app and get verified
- Invite your colleagues to Siilo
- Start collaborating!